LSB Steganography: A Complete Guide to Hiding Data in Images
I Built a very simple steganography encrypter and decrypter for PNG images using just basic Javascript and HTML Check it out here. The point of this article is to show people out there how browser malware extensions or just malicious websites can use steganography to hide the malicious and harmful code inside of images and only decode and use it when needed. For example, browser extensions trying to get their malicious extension published might use something like this in combination with general code obfuscation techniques to obfuscate the extractor from the moderators as well.
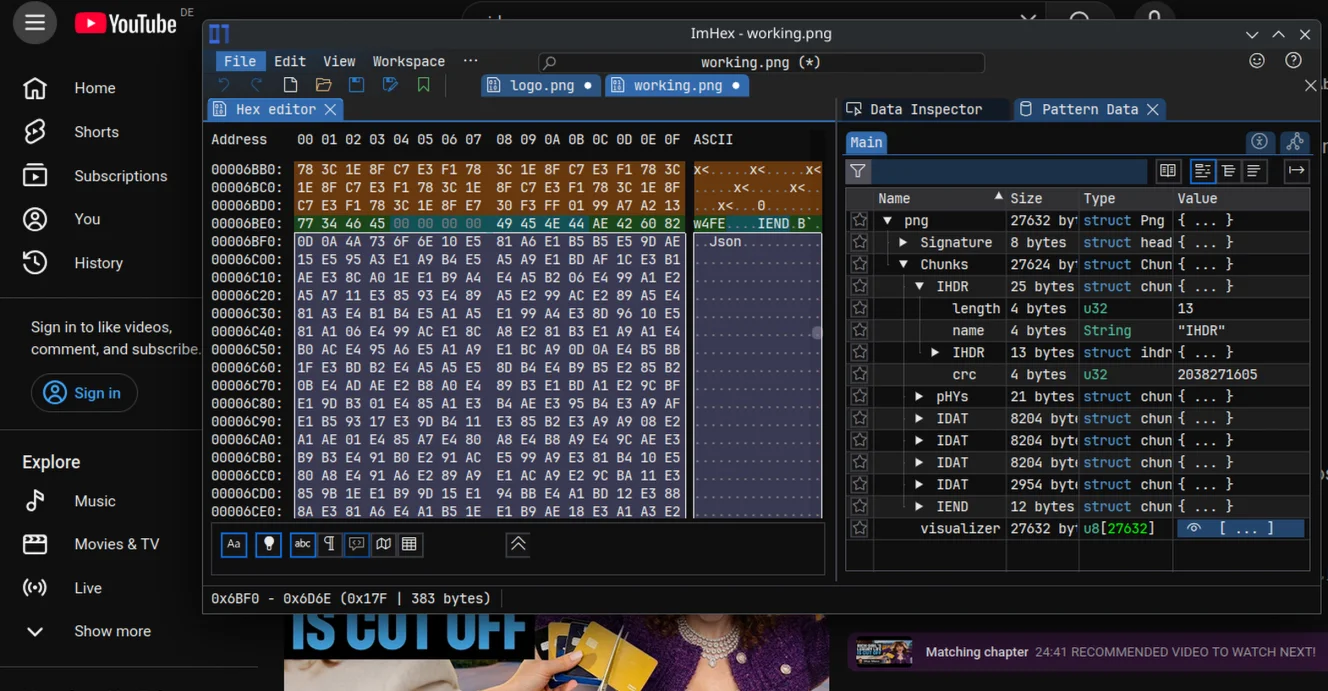
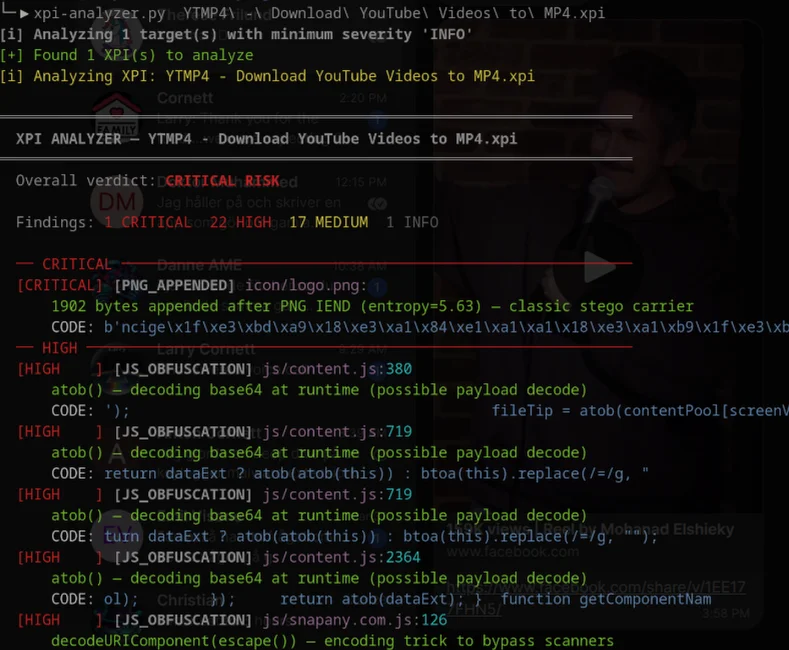
There was talk about some Firefox Extension using Steganography to hide base64 encoded javascript in malicious extensions not long ago - the sad part is, their method for steganography was more of an "paste block after PNG IEND characters signifies the end of the PNG file. In other words, you can barely call it stenography since they didnt' hide it in the images, they merely packed it together with an image, like a zip or tar.
In this article I will show you a real and very simple method called LSB Steganography. I have built a proof of concept that you can try for yourself here: LSB Steganography - https://www.yourdev.net/stego/index.html
For my next article I might post a deep dive malware analysis i made of a firefox extension which gave me the inspiration for this post
Or I might write a part 2 for this article, which goes into more complicated and sophisticated methods of steganography that even survives jpg compressions, and another method which makes it impossible to find a stego message within a picture unless you have the correct key so you know where to look. For simple implementations like this one, there are ways to detect it by statistical analysis
Introduction - What is steganography?
Steganography (in the context we will be discussing it here in this article) is the art of hiding messages or data within images.
Steganography — from the Greek steganos (covered) and graphein (writing) — is the practice of concealing messages within other non-secret data. Unlike cryptography, which scrambles a message to make it unreadable, steganography hides the existence of the message itself.
LSB (Least Significant Bit) steganography is one of the most popular and straightforward techniques for hiding data inside digital images. This method exploits the way pixel color values are stored to embed secret information in a way that is completely invisible to the human eye.
In this comprehensive guide, we'll explore:
- How digital images store color information
- The concept of the "least significant bit"
- Step-by-step encoding and decoding processes
- Practical applications and security implications
- Detection methods and countermeasures
Understanding Digital Images and Pixel Structure
How Pixels Store Color
A digital image is essentially a grid of pixels — tiny colored dots that, when viewed together, form a complete picture. Each pixel's color is represented by combining three primary colors: Red, Green, and Blue (RGB).
Each color channel is stored as a single byte (8 bits), giving us:
- Red (R): 0–255 (1 byte)
- Green (G): 0–255 (1 byte)
- Blue (B): 0–255 (1 byte)
Some image formats like PNG also include an Alpha (A) channel for transparency, making it RGBA with 4 bytes per pixel.
Example Pixel Breakdown
Let's say a pixel has the color RGB(72, 145, 200):
Red: 72 = 01001000 (binary)
Green: 145 = 10010001 (binary)
Blue: 200 = 11001000 (binary)
This gives us a bluish color. The key insight for LSB steganography is that these bytes have varying levels of importance.
The Concept of the Least Significant Bit
What is the LSB?
In an 8-bit byte, bits are numbered from 7 (most significant) to 0 (least significant):
Bit position: 7 6 5 4 3 2 1 0
Binary value: 1 0 0 1 0 0 0 1
↑ ↑
MSB (128) LSB (1)
- Most Significant Bit (MSB): Bit 7 — changing this bit changes the value by ±128
- Least Significant Bit (LSB): Bit 0 — changing this bit changes the value by ±1
Why the LSB Doesn't Matter Visually
Consider a red color channel with value 254:
- Binary:
11111110 - If we change the LSB from
0to1, we get 255:11111111
The visual difference between RGB(254, x, x) and RGB(255, x, x) is:
- 1/255 = 0.39% — completely imperceptible to the human eye
This tiny difference is what makes LSB steganography so effective. We can modify the LSB of every color channel in an image without creating any visible change.
How LSB Encoding Works
The Encoding Process
Here's the complete workflow for hiding a message inside an image:
Step 1: Prepare the Message
Convert your text message into bytes using UTF-8 encoding:
const message = "Hello!";
const encoder = new TextEncoder();
const msgBytes = encoder.encode(message); // Uint8Array [72, 101, 108, 108, 111, 33]
Step 2: Create a Length Header
To extract the message later, the decoder needs to know how many bytes to read. We prepend a 4-byte header containing the message length:
const lengthBuffer = new ArrayBuffer(4);
const lengthView = new DataView(lengthBuffer);
lengthView.setUint32(0, msgBytes.length, false); // big-endian, 32-bit unsigned int
const lengthBytes = new Uint8Array(lengthBuffer);
For a 6-byte message: [0, 0, 0, 6]
Step 3: Build the Full Payload
Concatenate the header and message:
const payload = new Uint8Array(4 + msgBytes.length);
payload.set(lengthBytes, 0); // bytes 0-3: length
payload.set(msgBytes, 4); // bytes 4+: message
Full payload: [0, 0, 0, 6, 72, 101, 108, 108, 111, 33]
Step 4: Convert Bytes to Bits
Each byte needs to be broken down into individual bits:
function bytesToBits(bytes) {
let bits = '';
for (const byte of bytes) {
for (let bitPos = 7; bitPos >= 0; bitPos--) {
bits += (byte >> bitPos) & 1; // extract each bit, MSB first
}
}
return bits;
}
The byte 72 (ASCII 'H') becomes: 01001000
Step 5: Embed Bits into the Image
For each bit in our payload, we modify one color channel's LSB:
let bitIndex = 0;
const stegoData = new Uint8ClampedArray(carrierImageData.data); // copy original pixels
for (let byteIndex = 0; byteIndex < stegoData.length && bitIndex < payloadBits.length; byteIndex++) {
// Skip alpha channels (every 4th byte: 3, 7, 11, 15...)
if (byteIndex % 4 === 3) continue;
const bit = parseInt(payloadBits[bitIndex]);
// Clear LSB: AND with 11111110 (0xFE)
// Set our bit: OR with 0 or 1
stegoData[byteIndex] = (stegoData[byteIndex] & 0b11111110) | bit;
bitIndex++;
}
The Magic Operation Explained:
Original byte: 10110111 (183)
AND with 0xFE: 11111110 (mask)
Result: 10110110 (182) — LSB cleared
Then OR with bit:
If bit = 1: 10110110 | 1 = 10110111 (183)
If bit = 0: 10110110 | 0 = 10110110 (182)
Step 6: Save as PNG
Export the modified pixel data as a PNG file (lossless format). JPEG would destroy the hidden data through lossy compression.
const dataURL = stegoCanvas.toDataURL('image/png');
How LSB Decoding Works
The Decoding Process
Extracting the hidden message is the reverse operation:
Step 1: Load the Stego Image
Read the pixel data into an array:
const ctx = canvas.getContext('2d');
ctx.drawImage(img, 0, 0);
const stegoImageData = ctx.getImageData(0, 0, img.width, img.height);
const data = stegoImageData.data;
Step 2: Extract All LSBs
Read the LSB from each R, G, B channel (skip alpha):
let extractedBits = '';
for (let byteIndex = 0; byteIndex < data.length; byteIndex++) {
if (byteIndex % 4 === 3) continue; // skip alpha
extractedBits += (data[byteIndex] & 1); // extract LSB only
}
The mask & 1 (binary 00000001) isolates bit 0:
10110111 & 00000001 = 00000001 = 1
10110110 & 00000001 = 00000000 = 0
Step 3: Read the Length Header
The first 32 bits encode the message length:
const headerBits = extractedBits.slice(0, 32);
const headerBytes = bitsToBytes(headerBits);
const headerView = new DataView(headerBytes.buffer);
const messageLength = headerView.getUint32(0, false);
Step 4: Extract the Message
Read exactly messageLength bytes after the header:
const messageBitsStart = 32;
const messageBitsEnd = 32 + messageLength * 8;
const messageBits = extractedBits.slice(messageBitsStart, messageBitsEnd);
Step 5: Convert Back to Text
const messageBytes = bitsToBytes(messageBits);
const decoder = new TextDecoder();
const message = decoder.decode(messageBytes);
And we recover: "Hello!"
Capacity Calculation
How Much Data Can You Hide?
Each pixel provides 3 usable bits (one from R, G, and B — we skip alpha to avoid transparency issues).
For an image with dimensions W × H:
- Total pixels:
W × H - Total bits available:
W × H × 3 - Total bytes available:
(W × H × 3) / 8 - Usable bytes (minus 4-byte header):
(W × H × 3) / 8 - 4
Example
A 1920×1080 Full HD image:
- Pixels: 2,073,600
- Bits: 6,220,800
- Capacity: ~777 KB of hidden data
A 4K image (3840×2160):
- Pixels: 8,294,400
- Bits: 24,883,200
- Capacity: ~3.1 MB of hidden data
Legitimate Use Cases
LSB steganography has several practical applications:
1. Digital Watermarking
Photographers and artists can embed copyright information or ownership metadata directly into images. Unlike traditional watermarks, LSB watermarks are invisible and survive most non-lossy editing operations.
2. Covert Communication
Journalists, activists, or individuals in oppressive regimes can use steganography to exchange sensitive information without attracting attention. An innocent-looking vacation photo could contain encrypted coordinates or meeting times.
3. Data Integrity Verification
Organizations can embed checksums or hash values inside images to detect tampering or corruption.
4. Anti-Counterfeiting
Physical products can be photographed with unique serial numbers hidden in product images, making it harder to create convincing counterfeits.
5. Secure Backup
Sensitive documents can be hidden inside family photos, providing an additional layer of security for backup storage.
Security Implications: The Dark Side
While steganography has legitimate uses, it's also exploited for malicious purposes:
Hiding Malware
Scenario: An attacker embeds malicious code inside an innocent-looking image file.
How It Works:
Payload Preparation: The attacker takes malware (e.g., a backdoor script, ransomware, or exploit code) and converts it to binary.
Encoding: Using LSB steganography, the malware is hidden in a seemingly harmless image — perhaps a meme, stock photo, or logo.
Distribution: The image is uploaded to social media, file-sharing sites, or sent via email. Security scanners see only an image file.
Extraction: The victim (or their compromised system) downloads the image. A decoder extracts the hidden payload.
Execution: The extracted code is executed, infecting the system.
Real-World Examples
Stegoloader (2014): A malware campaign that used LSB steganography to hide malicious PNG images on compromised websites. The images contained encrypted payloads that were extracted and executed.
Sunburst (2020): The SolarWinds supply chain attack used steganography techniques to hide command-and-control communications inside seemingly benign network traffic.
Invoke-PSImage: A PowerShell-based tool that embeds scripts inside PNG images using LSB techniques, used by penetration testers and attackers alike.
Why It's Effective for Attackers
Bypasses Detection: Most antivirus and intrusion detection systems scan for known malware signatures. A PNG file with slightly modified LSBs appears completely legitimate.
No File Type Mismatch: The file is genuinely an image — it opens in image viewers and passes file type validation.
Evades Content Filters: Email filters and web proxies allow image files through without deep inspection.
Low Suspicion: Users and security teams don't typically suspect vacation photos, company logos, or meme images.
Detection and Countermeasures
Steganalysis: Detecting Hidden Data
While LSB steganography is hard to spot visually, statistical analysis can reveal its presence:
1. Chi-Square Attack
Natural images have predictable statistical properties in their LSB distributions. Hidden data creates anomalies that chi-square tests can detect.
2. RS (Regular-Singular) Analysis
This technique analyzes how pixel values change when LSBs are flipped. Stego images show different patterns than clean images.
3. Histogram Analysis
Embedding data in LSBs can create subtle irregularities in color histograms, particularly in low-entropy regions.
4. Sample Pair Analysis (SPA)
Examines pairs of sequential pixel values to detect LSB manipulation.
Defensive Measures
For Organizations:
Image Reprocessing: Convert all uploaded images to JPEG with moderate compression — this destroys LSB data while maintaining visual quality.
Metadata Stripping: Remove EXIF data and reprocess images to eliminate potential steganographic payloads.
Deep Packet Inspection: Monitor for tools like
steghide,zsteg, or custom decoders in network traffic.Machine Learning Models: Train classifiers to detect stego images based on statistical anomalies.
For Security Researchers:
Tools for detecting LSB steganography:
- StegExpose: Automated steganalysis tool using machine learning
- zsteg: Ruby-based detector for LSB data in PNG and BMP files
- stegdetect: Classic tool for detecting various steganography methods
- OpenStego: Open-source steganography suite with detection capabilities
Limitations of LSB Steganography
Despite its effectiveness, LSB steganography has weaknesses:
Fragile to Compression: Lossy formats (JPEG) destroy LSB data completely.
Fragile to Resizing: Resizing or cropping removes or scrambles hidden data.
Fragile to Rotation: Even rotating by 90° can corrupt the payload.
Statistical Detection: Advanced steganalysis can identify stego images with high accuracy.
Limited Capacity: Large payloads require large images or multiple carrier files.
Advanced Techniques and Variations
Randomized LSB Embedding
Instead of sequential embedding, use a pseudo-random sequence generator (PRNG) with a shared seed to scatter bits across the image. This makes detection harder and increases robustness.
// Use a seeded PRNG to select pixel positions
function getRandomPixelSequence(seed, length) {
const rng = seedRandom(seed);
const sequence = [];
const available = Array.from({length}, (_, i) => i);
for (let i = 0; i < available.length; i++) {
const j = Math.floor(rng() * available.length);
sequence.push(available.splice(j, 1)[0]);
}
return sequence;
}
Multi-Bit LSB
Instead of only the least significant bit, use the 2 least significant bits (bits 0 and 1). This doubles capacity but increases detectability.
Adaptive LSB Embedding
Only embed data in "busy" regions of the image (high-frequency areas with lots of detail). Smooth gradients and solid colors are left untouched, making detection much harder.
Encrypted Payloads
Always encrypt your payload before embedding:
// Encrypt before encoding
const encrypted = CryptoJS.AES.encrypt(message, password).toString();
const msgBytes = encoder.encode(encrypted);
This provides defense in depth: even if the hidden message is discovered, the attacker still needs to decrypt it.
Code Implementation Example
Here's a minimal Python implementation:
from PIL import Image
import numpy as np
def encode_lsb(image_path, message, output_path):
"""Encode message into image using LSB steganography."""
img = Image.open(image_path).convert('RGB')
pixels = np.array(img)
# Prepare payload: 4-byte length header + message bytes
msg_bytes = message.encode('utf-8')
length_bytes = len(msg_bytes).to_bytes(4, byteorder='big')
payload = length_bytes + msg_bytes
# Convert to bits
bits = ''.join(format(byte, '08b') for byte in payload)
# Flatten pixel array and embed bits
flat = pixels.flatten()
if len(bits) > len(flat):
raise ValueError("Message too large for image")
for i, bit in enumerate(bits):
flat[i] = (flat[i] & 0xFE) | int(bit)
# Reshape and save
stego_pixels = flat.reshape(pixels.shape)
stego_img = Image.fromarray(stego_pixels.astype('uint8'))
stego_img.save(output_path, 'PNG')
def decode_lsb(image_path):
"""Decode message from stego image."""
img = Image.open(image_path).convert('RGB')
pixels = np.array(img).flatten()
# Extract LSBs
bits = ''.join(str(pixel & 1) for pixel in pixels)
# Read length header (first 32 bits)
length = int(bits[:32], 2)
# Extract message bits
msg_bits = bits[32:32 + length * 8]
# Convert to bytes then string
msg_bytes = bytes(int(msg_bits[i:i+8], 2) for i in range(0, len(msg_bits), 8))
return msg_bytes.decode('utf-8')
# Usage
encode_lsb('carrier.png', 'Secret message!', 'stego.png')
message = decode_lsb('stogo.png')
print(message) # Output: Secret message!
Best Practices
For Legitimate Use:
- Always use PNG or BMP — never JPEG for steganography
- Encrypt before embedding — use AES-256 or similar
- Use high-resolution images — more capacity, harder to detect
- Add noise intentionally — makes statistical analysis harder
- Don't reuse carrier images — use fresh images each time
For Security:
- Assume images may contain hidden data — especially from untrusted sources
- Reprocess uploads — convert to JPEG or add watermarks to destroy LSB data
- Monitor for extraction tools — detect steghide, zsteg, etc. in your environment
- Educate users — awareness of steganography threats
- Use steganalysis tools — scan suspicious images regularly
Conclusion
LSB steganography is a fascinating intersection of information theory, digital image processing, and security. Its simplicity makes it accessible to beginners, yet its effectiveness keeps it relevant in both legitimate privacy applications and malicious attack campaigns.
The technique exploits a fundamental property of human vision — our inability to perceive tiny color changes — to hide data in plain sight. While powerful, it's not invincible: statistical analysis, image reprocessing, and machine learning detection continue to evolve.
Key Takeaways:
✓ LSB steganography hides data in the least significant bits of pixel color values
✓ Changes are invisible (<0.4% color difference per channel)
✓ Capacity is approximately (width × height × 3) / 8 bytes
✓ PNG format is required — JPEG destroys LSB data
✓ Has both legitimate uses (watermarking, covert comms) and malicious uses (malware hiding)
✓ Detectable through statistical analysis and steganalysis tools
✓ Best combined with encryption for security
Whether you're a security researcher, digital forensics investigator, privacy advocate, or curious developer, understanding LSB steganography gives you insight into one of the most elegant techniques for hiding information in the digital age.
Further Reading
Academic Papers:
- "Detecting LSB Steganography in Color and Grayscale Images" (Fridrich et al.)
- "Reliable Detection of LSB Steganography in Color and Grayscale Images" (Harmsen & Pearlman)
Tools and Libraries:
- Steghide: Popular cross-platform steganography tool
- OpenStego: Java-based open-source suite
- Stegpy: Python implementation
- LSBSteg: Python library for LSB techniques
Standards and Specifications:
- PNG Specification (ISO/IEC 15948)
- JPEG vs. PNG: Lossy vs. Lossless Compression
Stay curious, stay secure.
Don't forget to check out the working example: https://www.yourdev.net/stego/index.html
Author's Note: This article is for educational purposes. Always use steganography ethically and legally. Unauthorized embedding of data in others' images or systems may violate laws such as the Computer Fraud and Abuse Act (CFAA) or equivalent legislation in your jurisdiction.
Need an Android Developer or a full-stack website developer?
I specialize in Kotlin, Jetpack Compose, and Material Design 3. For websites, I use modern web technologies to create responsive and user-friendly experiences. Check out my portfolio or get in touch to discuss your project.